Update
The second part of this hack will stop working when the BBC get around to rolling out HTTPS at some point in the next year (second update: over a year after this post was written and it still hasn’t been done). This is good news! You should still be able to block the banner though.
About time! The website of the guardian has supported HTTPS for ages. Their videos also work without without flash (workaround for BBC News videos) and the URLs are actually descriptive too.
This may be a fun demonstration, but it shows the dangers of not using HTTPS everywhere and of cross-site scripting (XSS). There are those that argue HTTPS is not required for read-only sites but altering what people see can be problematic (for example, maybe someone is replacing adverts on the site and stealing revenue).
Here is another amusing example of where the script matched too much. I particularly like the use of stock photos for those who don’t know what trumpets and bagpipes look like. I’d fix this to match only whole words but it’s quite funny and it will stop working “soon” anyway.
If you’re interested in any of these topics then you may want to take a look at my book.
I’ve previously covered how to block the BBC News website Breaking News pop-up banner. This works well on laptops and desktops but is trickier on locked-down devices, such as phones and tablets. Here’s how to block this in one place for all devices on your network, and even when you’re out and about.
DNS
The key to this is hijacking the DNS lookup for the domain polling.bbc.co.uk. In the previous guide we did this by editing the hosts file on the local machine, but now we need to do it at the DNS (Domain Name System) server level to block it for all devices on the network.
If you don’t already have a DNS server on your network then you will need to set one up. I use dnsmasq running on a Raspberry Pi, but if you don’t want to configure this manually then there are projects designed for blocking adverts, such as Pi-hole, that make this easier. If your router doesn’t support altering the DNS server addresses then you will need to configure dnsmasq to take over DHCP duties too.
Then add an entry that will stop the polling domain from being resolved to the correct IP address.
0.0.0.0 polling.bbc.co.uk
This will prevent the Breaking News banner from being displayed by any device on your network when you visit the BBC News website on them. However, this will only work while they are connecting to the internet through your network, and we can do better than that.
Caching
To make this continue to work after devices have left your network we need to use caching, both at the DNS level and at the HTTP level.
TTL
The first step is to set a high TTL (Time To Live) value on the DNS entry. This will ensure that devices cache the IP address and use the value you have set, even after disconnecting from your WiFi (e.g. when on 4G). This may be sufficient for you, but the TTL can’t typically be set longer than one day. To cache for longer we need to take things further.
HTTP
As the BBC fails to use HTTPS, we can hijack the connection and serve whatever content we want.

You can get Chrome to obviously indicate this by toggling the chrome://flags/#mark-non-secure-as flag, which will probably become the default fairly soon.
For example, we can serve a dummy banner, hidden using an inline CSS style (display: none;). The easy way is to use my ready made host for this, by adding this entry to your DNS instead of blocking the domain.
192.30.252.153 polling.bbc.co.uk
This will use a GitHub page to serve the following JSON response.
breakingNews({
"pollPeriod": 30000,
"isError": false,
"html": "<div style=\"display: none;\" class=\"falcon\">\n<div class=\"falcon__inner\">\n<a href=\"https://chrome.google.com/webstore/detail/drumpfinator/hcimhbfpiofdihhdnofbdlhjcmjopilp\" target=\"_blank\" class=\"falcon__link\" data-asset-id=\"What did you expect, sparks?\">\n<h2 class=\"falcon__badge\">OMG, Breaking News‽<span class=\"off-screen\"><\/span><\/h2>\n<p class=\"falcon__heading\"><\/p>\n<\/a>\n<button class=\"falcon__button\">\n<span class=\"off-screen\">Close breaking news<\/span>\n<\/button>\n<\/div>\n<\/div><script async=\"async\">var mainpage = document.getElementById(\'page\');Drumfinate(mainpage.getElementsByTagName(\'h1\'));Drumfinate(mainpage.getElementsByTagName(\'h3\'));Drumfinate(mainpage.getElementsByTagName(\'li\'));Drumfinate(mainpage.getElementsByTagName(\'p\'));Drumfinate(mainpage.getElementsByTagName(\'figcaption\'));function Drumfinate(list) {for(var i = 0; i < list.length; i++){if(list[i].innerHTML.indexOf(\'Trump\') != -1){list[i].innerHTML = list[i].innerHTML.replace(\/Trump\/g,\'Drumpf\');}}}<\/script>"
});
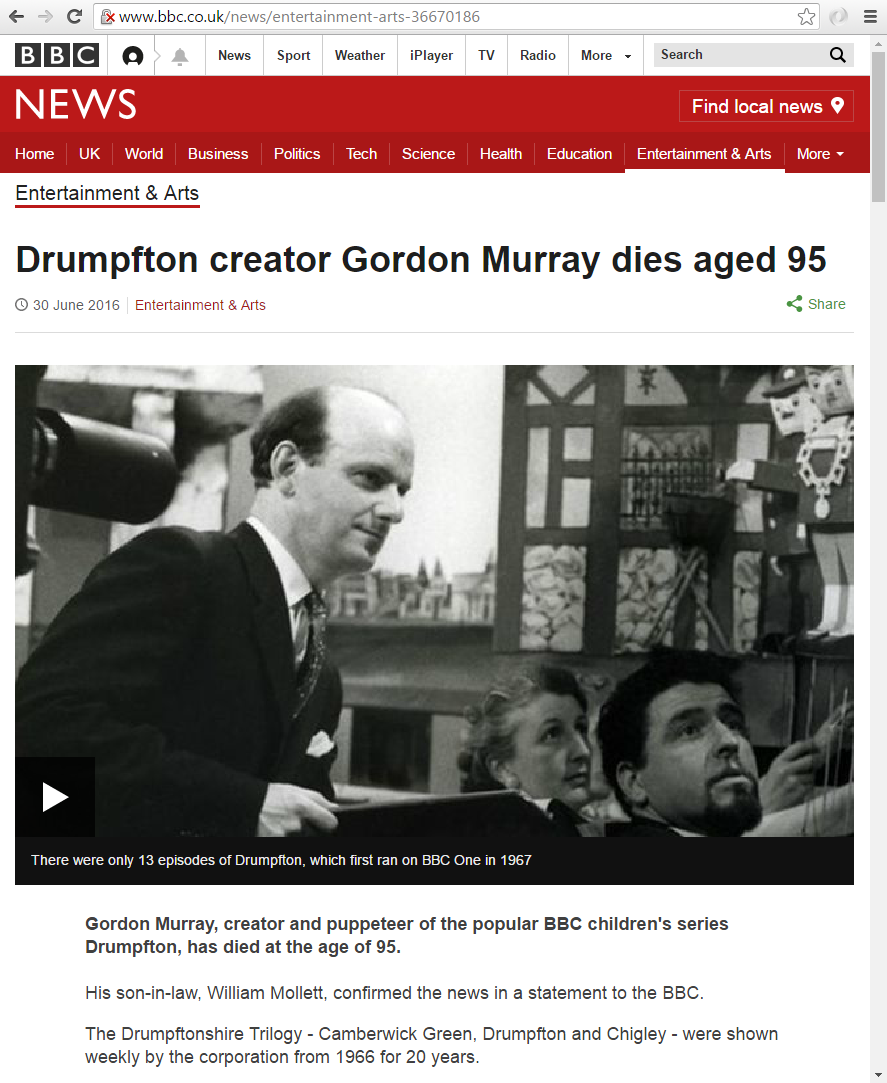
The observant among you may notice that this also injects some JavaScript. This replaces all instances of Trump with Drumpf, which doesn’t always work exactly as expected.
This is just a fun example, but it shows the dangers of not using HTTPS everywhere.
Some ISPs (I’m looking at you BT) also hijack your internet connection. So you may find that your request doesn’t always get through and is served by one of their caching proxy servers. They must be doing some deep packet inspection as the connection isn’t configured to use a proxy.
In this case you will need to host the fake response on your local network and use a DNS entry that points to the web server on your LAN.
192.168.0.2 polling.bbc.co.uk
Change 192.168.0.2 to the IP address of this server, which could be the same as the DNS/DHCP server (not 127.0.0.1).
This also allows you to configure HTTP caching on the response. For example, if using apache then you can add the following to a .htaccess file in the directory to instruct browsers to cache the response for a year.
Header set Cache-Control "max-age=31536000, public"
If you want to read more about this then I cover both HTTP caching, HTTPS and DNS in my book.